Melindungi Debian 10 Server Pakai Sshguard Dan Firewalld
Posted on
Salah satu kewajiban dalam ngurus server adalah mengamankan jalur masuk ke server, yakni SSH. Salah satu cara untuk mengamankan akses SSH adalah dengan memakai sshguard. SSH guard berkeja dengan cara melakukan monitor terhadap log SSH dan melakukan tindakan pemblokiran terhadap IP yang berkali-kali gagal auth dengan memanfaatkan firewall yang ada pada system misalnya iptables, nftables, atau interface lebih tinggi yakni firewalld atau ufw.
sshguard is an intrusion prevention system that parses server logs, determines malicious activity, and uses the system firewall to block the IP addresses of malicious connections. sshguard is written in C so it does not tax an interpreter. -- wiki gentoo
sshguard protects hosts from brute-force attacks against SSH and other services. It aggregates system logs and blocks repeat offenders using one of several firewall backends, including
iptables,ipfw, andpf. -- sshguard.net
Aku secara pribadi lebih suka plain iptables, lebih mudah untuk custom rule aneh-aneh. Namun, semenjak debian 10 beralih ke nftables, aku lari ke firewalld. Sebab, aku belum begitu memahami nftables. Firewalld versi terakhir sudah mendukung nftables, makanya aku pakai firewalld aja.
Firewalld provides a dynamically managed firewall with support for network/firewall zones that define the trust level of network connections or interfaces. It has support for IPv4, IPv6 firewall settings, ethernet bridges and IP sets. There is a separation of runtime and permanent configuration options. It also provides an interface for services or applications to add firewall rules directly. -- firewalld.org
Oleh sebab aku pakai Debian 10 dan Firewalld, maka beginilah proses instalasi dan konfirgurasi sshguard
Pertama, tentu aku install paket sshguard
apt update
apt install sshguard
Kedua, config sshguard supaya pakai backend firewalld
nano /etc/sshguard/sshguard.conf
# isinya setelah aku edit
#### REQUIRED CONFIGURATION ####
# Full path to backend executable (required, no default)
# aku pakai firewalld
BACKEND="/usr/lib/x86_64-linux-gnu/sshg-fw-firewalld"
# Shell command that provides logs on standard output. (optional, no default)
# Example 1: ssh and sendmail from systemd journal:
LOGREADER="LANG=C /bin/journalctl -afb -p info -n1 -o cat SYSLOG_FACILITY=4 SYSLOG_FACILITY=10"
#### OPTIONS ####
# Block attackers when their cumulative attack score exceeds THRESHOLD.
# Most attacks have a score of 10. (optional, default 30)
THRESHOLD=30
# Block attackers for initially BLOCK_TIME seconds after exceeding THRESHOLD.
# Subsequent blocks increase by a factor of 1.5. (optional, default 120)
# Blokir selama 24 hours (60480 seconds)
BLOCK_TIME=60480
# Remember potential attackers for up to DETECTION_TIME seconds before
# resetting their score. (optional, default 1800)
# Track IP addresses selama 24 hours (60480 seconds)
DETECTION_TIME=60480
# IP addresses listed in the WHITELIST_FILE are considered to be
# friendlies and will never be blocked.
WHITELIST_FILE=/etc/sshguard/whitelist
Ketiga, restart dan enable service sshguard
systemctl restart sshguard
systemctl enable sshguard
Kalau mau melihat sshguard beraksi, silakan pakai journalctl
root@wiki:/home/sumar# LANG=C /bin/journalctl -afb -p info -n1 -o cat SYSLOG_FACILITY=4 SYSLOG_FACILITY=10
Contoh outputnya dapat dilihat digambar
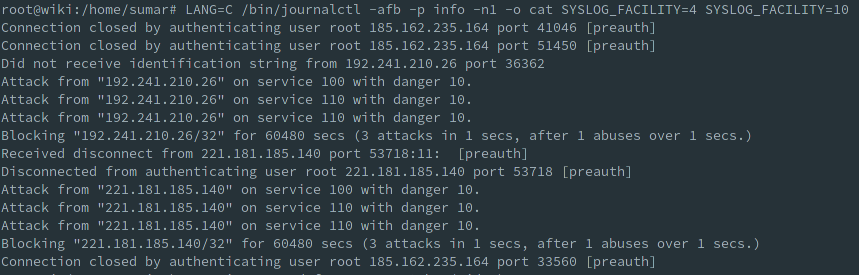
Dari gambar nampak:
...
Blocking "192.241.210.26/32" for 60480 secs (3 attacks in 1 secs, after 1 abuses over 1 secs.)
...
Blocking "221.181.185.140/32" for 60480 secs (3 attacks in 1 secs, after 1 abuses over 1 secs.)
Itu artinya sshguard sudah berjalan sebagaimana mestinya.
Untuk cek daftar IP Address yang terblokir gunakan perintah:
root@wiki:/home/sumar# firewall-cmd --info-ipset=sshguard4
# outputnya
sshguard4
type: hash:net
options: family=inet
entries: 192.241.210.26/32 221.181.185.140/32 221.131.165.124/32 221.181.185.223/32 139.59.144.132/32 81.161.63.254/32 62.221.121.185/32
Sekali lagi konteksnya aku pakai debian 10, nftables, dan firewald.
Cool~